Cyber
KAPE Quarterly Update - Q4 2023
by Andrew Rathbun, Eric Zimmerman

With KAPE, you can find and prioritize the most critical systems to your case and collect key artifacts before imaging.
This means no longer having to wait until full system images are gathered and then wading through data where typically less than 10% will have any forensic value.
"The gist of [KAPE] is that in as little as half an hour, we can go from disk imaging to substantive analysis of filesystem, shell, execution, event, and registry data."
Troy Larson, Microsoft
Screening and Monitoring
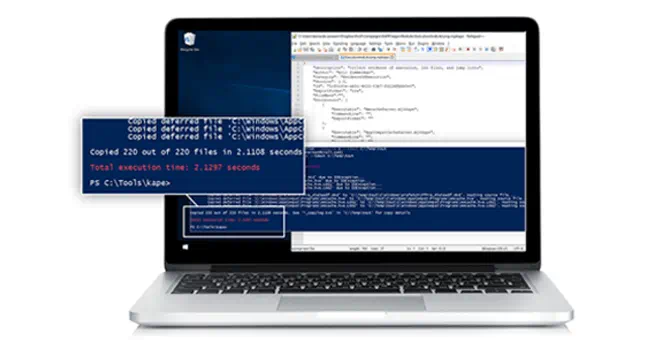
KAPE has two primary phases – target collection and module execution:
KAPE gives you access to targets and modules for the most common operations required in forensic exams, helping investigators gather a wider range of artifacts in a fraction of the time, enriching evidentiary libraries.
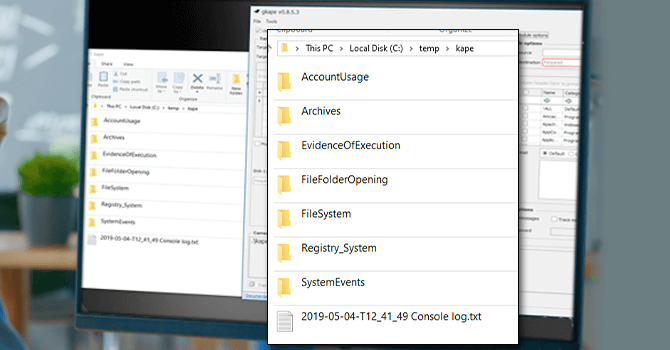
KAPE focuses on collecting and processing relevant data quickly, grouping artifacts in categorized directories such as EvidenceOfExecution, BrowserHistory and AccountUsage. Grouping things by category means an examiner no longer needs to know how to process prefetch, shimcache, amcache, userassist, etc., as they relate to evidence of execution artifacts.
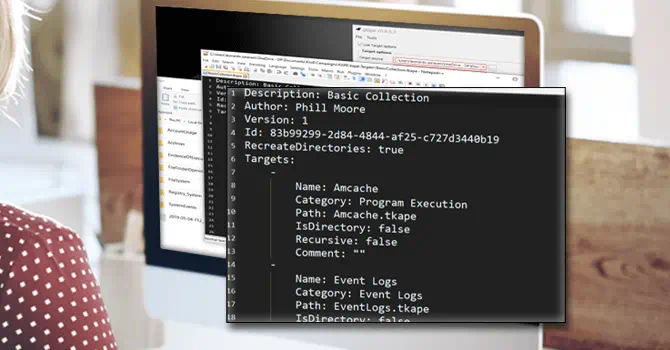
When handling an incident, forensic examiners are tasked with knowing which artifacts to collect, where they may reside, and how to collect the data without damaging the evidence or chain of custody. With KAPE, forensic examiners have a solution to find, collect and process forensic artifacts in a way that standardizes forensic engagements by leveraging a wider range of extracted artifacts. KAPE can also help facilitate the onboarding and training of new investigators by standardizing and scaling artifact pulls.

Eric Zimmerman and a team of Kroll experts structured a hands-on course to lead forensic examiners to KAPE mastery, enabling federal agents, law enforcement personnel, first responders, digital forensic analysts and incident response team members to:
Kroll works on some of the most complex and highest profile cyber incidents in the world and performs digital forensics and evidence collection for thousands of companies. This unique frontline insight from our experts is enhanced by input from the global DFIR community to actively contribute to the development of KAPE. To learn more:
Read more about KAPE enterprise licenses here.
Learn how to jumpstart your forensic investigations and find meaningful data fast with a live KAPE training session led by a Kroll instructor.
For individuals or business interested in using KAPE for commercial purposes.
The latest KAPE tutorials, webcasts and guides created by Kroll instructors.
by Andrew Rathbun, Eric Zimmerman

by Andrew Rathbun, Eric Zimmerman

by Eric Zimmerman, Andrew Rathbun

by Eric Zimmerman, Andrew Rathbun

Join Kroll experts at the RSA Conference in San Francisco May 6-9, 2024. Stop by booth 2239 in the South Expo Hall to meet our team.

Join the Q1 2024 Cyber Threat Landscape Virtual Briefing as Kroll’s cyber threat analysts outline notable trends and insights from our incident response intelligence.

Join Kroll experts, along with Nike Trost and Howard Cornwell from the FCA, as they share insights on the regulatory landscape and its implications for the alternatives and asset management industry.




