KAPE has seen a number of key updates during the third quarter of this year. The guide below, assembled by our team of experts, highlights all the important changes that have occurred from July through September 2021.
Key Q3 2021 KAPE Updates
- Project boards established on GitHub for all KAPE-related repositories
- RegistryHivesOther Target created to cover uncommon Registry hives
- Kape Research Modules were highlighted in previous 2021 quarterly updates, but they’ve continued to grow with the addition of the aforementioned RegistryHivesOther Target
- Exportfile added to SrumECmd and SumECmd modules for better end user awareness
See end of the article for additional updates.
Project Boards Established on GitHub for all KAPE-Related Repositories
Kanban boards were created for multiple GitHub repositories. As a result, Kroll’s ongoing tasks regarding KAPE have been transposed into the public realm into these Kanban boards, allowing anyone to see what’s ahead on the roadmap. These boards are also available to the public for contribution. For further information, reach out to [email protected].
Below are direct links to the respective GitHub project boards:
- KAPE Targets/Modules To Do List
- KAPE Documentation To Do List
- Registry Explorer/RECmd Plugins
- RECmd Kroll Batch File To Do List
- SQLECmd Maps Ideas
- EvtxECmd Maps Ideas
Phill Moore sparked this idea. Be sure to follow his passion project, This Week in 4n6.
RegistryHivesOther Target Created to Cover Uncommon Registry Hives
During a recent revision of the Kroll Batch File for RECmd, unfamiliar Registry hives were uncovered, so the Kroll team developed a RegistryHivesOther Compound Target to cover the following Registry hives:
- BBI
- BCD-Template
- COMPONENTS
- DEFAULT
- DRIVERS
- ELAM
- userdiff
- VSMIDK
The forensic significance of these hives is currently unknown, so they are NOT included in the RegistryHives Compound Target. A note indicating as such has been included in the Compound Target for greater visibility.
KapeResearch Modules Were Highlighted in Previous 2021 Quarterly Updates, But They’ve Continued to Grow with The Addition of The Aforementioned Registryhivesother Target
KapeResearch Modules were created for the aforementioned Registry hives that are covered within the RegistryHivesOthers Compound Target. This will allow for those who want to do research into these hives to do so with a recursive dump from the ROOT (or topmost) key within the Registry hive.
Exportfile Added to SrumECmd and SumECmd Modules for Better End-User Awareness
Combining the KapeTriage Compound Target and !EZParser Compound Module are a common workflow with KAPE users. If an artifact listed within the KapeTriage Compound Target, every single EZ Tool listed within the !EZParser Compound Module will be put to work and provide output. Over time, Kroll has noticed that two tools in particular, SrumECmd and SumECmd, did not provide output using this workflow due to the nature of ESE databases needing to be repaired when acquired from a live system. This is a manual process that is highlighted here.
As a result, end-users may have mistaken an empty output folder for those respective Modules as absence of the artifact when that was not actually the case. Therefore, Export File has been added to each of those Modules for the purpose of outputting the console output to a text file regardless of whether the tool(s) parses the artifact(s) successfully. The reason for this is to provide greater visibility to the end-user about whether a) the artifact exists, b) it was parsed successfully, and if not, c) what they can do to ensure it does get parsed successfully. Feedback on this addition to these Modules has been universally positive. The SRUM and SUM databases are invaluable artifacts for data exfiltration and lateral movement, respectively, in the incident response world.
The community has continued to contribute to the KapeFiles repository, which is greatly appreciated! The functionality of KAPE continues to grow with your support!
For anyone looking to learn more about digital forensics, to develop a better workflow or to become more comfortable with the command line and CSVs rather than GUIs, our experts strongly recommend running KAPE on their own system. Start with either !BasicCollection or KapeTriage for Targets and use !EZParser on for Modules. Examine the output in Timeline Explorer, another tool created by Eric, and learn what and how your systems record artifacts. If you have any questions about KAPE, please email [email protected].
Here is an overview of the changes to the KapeFiles GitHub repository from July 1, 2021, to September 30, 2021.
Targets Added/Updated
- $J.tkape
- AnyDesk.tkape
- CloudStorage.tkape
- EventTraceLogs.tkape
- EventTranscriptDB.tkape
- Kaseya.tkape
- MicrosoftTeams.tkape
- Nicotine++.tkape
- pCloudDatabase.tkape
- RegistryHivesOther.tkape
- ServerTriage.tkape
- SOFELK.tkape
- SQLDatabases.tkape
- SUM.tkape
- WebServers.tkape
- WindowsTelemetryDiagnosticsLegacy.tkape
Modules Added/Updated
- bstrings.mkape
- bstrings_AeonWallet.mkape
- bstrings_BitCoinWallet.mkape
- bstrings_Bitlocker.mkape
- bstrings_ByteCoinWallet.mkape
- bstrings_CreditCards.mkape
- bstrings_CryptoWallets.mkape
- bstrings_DashCoinWallet.mkape
- bstrings_DashCoinWallet2.mkape
- bstrings_Email.mkape
- bstrings_FantomCoinWallet.mkape
- bstrings_IPv4.mkape
- bstrings_MACAddresses.mkape
- bstrings_MoneroWallet.mkape
- bstrings_SSN.mkape
- bstrings_SumoKoinWallet.mkape
- bstrings_UNC.mkape
- bstrings_URLs.mkape
- bstrings_USPhone.mkape
- bstrings_WinPath.mkape
- bstrings_ZipCodes.mkape
- Chainsaw.mkape
- Get-DoSvc4n6.mkape
- KapeResearch
- Additions
- KapeResearch_Registry_BBI.mkape
- KapeResearch_Registry_BCD-Template.mkape
- KapeResearch_Registry_COMPONENTS.mkape
- KapeResearch_Registry_DEFAULT.mkape
- KapeResearch_Registry_DRIVERS.mkape
- KapeResearch_Registry_ELAM.mkape
- KapeResearch_Registry_userdiff.mkape
- KapeResearch_Registry_VSMIDK.mkape
- Updates
- Added ROOT functionality from a recent RECmd update to recursively dump the entire contents of a given hive to JSON
- SOFELK_Parser.mkape
- SOFELK_Parser_EvtxECmd.mkape
- SOFELK_Parser_LEcmd.mkape
- SOFELK_Parser_MFTECmd.mkape
- SOFELK_Parser_PECmd.mkape
KAPE-Related GitHub Repositories
Our experts recommend “watching” the following GitHub repositories for KAPE-related updates:
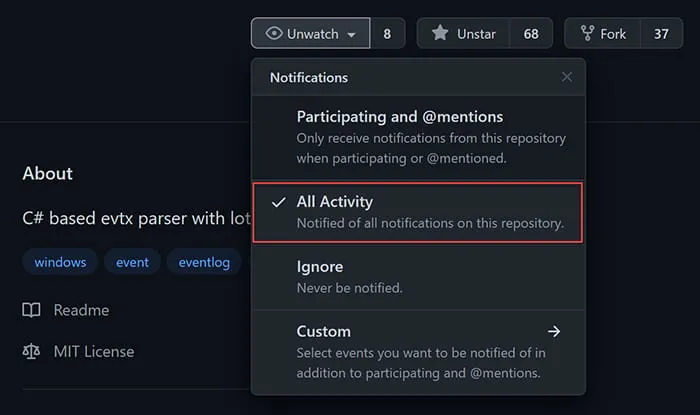
- KAPE Targets and Modules
- Registry Explorer/RECmd Plugins
- RECmd Batch Files
- SQLECmd Maps
- EvtxECmd Maps
- All of Eric Zimmerman's GitHub Repositories
If you need additional KAPE support, explore our virtual live training and certification opportunities or contact our experts at [email protected]. An enterprise license is required when KAPE is used on a third-party network and/or as part of a paid engagement.
This article was written by Andrew Rathbun, a Senior Associate in Kroll's Cyber Risk practice.








