Kroll has observed an uptick in actors offering network access on the dark web, particularly in the wake of recent disruptions to the ransomware-as-a-service (RAAS) ecosphere such as the ban on ransomware discussions in notorious underground criminal forums.
Understanding the Initial Access Broker Process
Threat actors who offer network access, known as initial access brokers, operate at the beginning of the intrusion lifecycle by conducting reconnaissance to identify networks with vulnerable applications or devices, including Virtual Private Network (VPN) appliances, servers with exposed software vulnerabilities or open Remote Desktop Protocol (RDP). During the last year, multiple VPN providers have announced critical vulnerabilities, many of which could be exploited by attackers to access sensitive data such as login credentials. Open RDP instances are often exploited by actors testing credentials via brute-force attacks such as password spraying or by actors testing credentials related to the target network which are publicly exposed in credential dumps on the dark web.
Once access is achieved, access brokers advertise their network access on dark web forums, seeking to sell the validated credentials to ransomware operators, affiliates or other criminals who leverage the initial access to conduct a number of different cyber attacks such as data theft or encryption. In particular, ransomware operators are known to purchase such listings and provide them to their affiliate distributors who then engage in the intrusion lifecycle to execute code on the target network for lateral movement, conduct privilege escalation and ultimately, mission execution in the form of data theft, data destruction or ransomware deployment.
This segmented approach of RAAS operators creates more layers of intermediaries between the operators and the actors on the ground who carry out the attack, decreasing the risk of exposure and law enforcement apprehension.
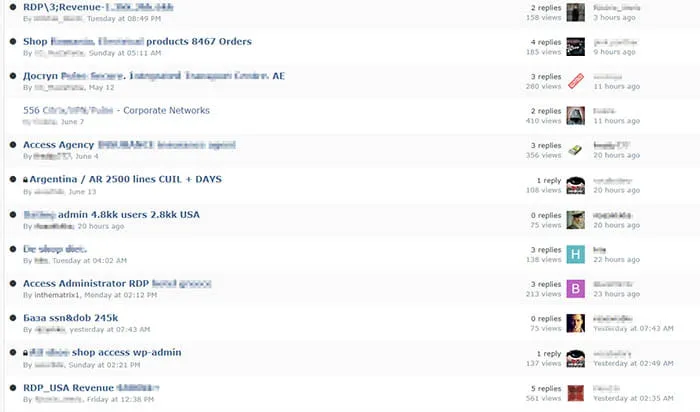
Figure 1 illustrates an auction page in a dark web marketplace advertising RDP/VPN credentials
Kroll Observations
In incident response investigations, our digital forensic examiners often identify a single suspicious VPN or RDP log-in that predates the ransomware activity by several days, weeks or, at times, months. That first suspicious log-in is likely to be the initial access broker testing credentials and identifying a “match” for a username and password combination. The user account or internal user’s computer that the unauthorized actor first lands on as a result of the log in success is what investigators associate with “patient zero” for the incident investigation. Subsequent analysis of the target organization domain has frequently identified that the credentials related to “patient zero” were readily available in various credentials dumps posted to the dark web.
Example Engagement
Multiple times in the past year, Kroll has observed threat actors in dark web forums sharing large datasets related to confirmed credentials for various VPN applications. In August 2020, a technology company experienced a ransomware attack. That same month, a large dataset of VPN credentials was briefly posted on a dark web forum. Kroll’s identification and review of that dataset identified multiple account credentials available from the organization’s employees, matching up nearly 100% with the accounts that the threat actors had accessed during the attack. This illustrated the likelihood that actors conducting ransomware attacks have access to initial lists of legitimate credentials, highlighting how dark web postings assist ransomware threat actor groups and organized crime affiliates to repeat their intrusion lifecycles against victims.
Expert’s Corner
Keith Novak, Managing Director, Kroll Cyber Risk, provides best practices to mitigate against the effectiveness of initial access brokers:
- Awareness Training
Training employees to identify and report phishing emails remains a critical component of every organization’s security defenses. An organization should build on employee training with technical response procedures that guide the IT or InfoSec teams on the investigation and response to phishing attempts. - Multi-Factor Authentication (MFA)
MFA pairs a username and password with a unique second factor which can include a PIN or biometric that prevents an attacker who obtained user credentials from logging in as a legitimate employee. MFA should be required for all remote access, cloud services, and privileged access accounts and remains one of the top recommendations for any organization. - Vulnerability Management
Actor groups don’t always rely on phishing to obtain their access. In fact, many threat actor groups exploit unpatched public facing systems and services to gain their initial foothold and exfiltrate usernames and passwords from internal systems that have been compromised. A mature vulnerability management program should include routine scanning of all external and internal systems, devices, and applications for vulnerable software and the timely application of patches from the vendors to remediate them. -
Public Facing Systems
Reducing an organization’s public facing systems and services is a great way to reduce the risk of initial compromise. For example, attackers routinely target Microsoft RDP services for both vulnerabilities as an entry point using phished user credentials. Moving all remote access services behind a corporate remote access VPN connection, requiring MFA, and posture-checking the users’ device can be very effective at defending against unauthorized access - Passwords
When it comes to password best practices, a few concepts continue to be proven true including: requiring the use of MFA, the longer the password the better, utilizing password managers, preventing the caching of passwords on user systems and browsers, and not sharing credentials with others. - Digital Risk Protection (DRP)
Proactive monitoring of dark web forums and other remote corners of the internet can help spot when corporate credentials are exposed in a new auction, or if attackers are impersonating your domains for phishing campaigns. Consider incorporating DRP in your security program. proven true including: requiring the use of MFA, the longer the password the better, utilizing password managers, preventing the caching of passwords on user systems and browsers, and not sharing credentials with others.
To protect your access credentials and prevent them from possibly appearing on the dark web for auction, it is important to set up proper precautions including ensuring good password hygiene and enabling MFA. Kroll’s Digital Risk Protection services can be used to monitor the deep and dark web for any exposures including any access credentials from your organization. Our experts will monitor for any threats, and provide assessments of exposure and vulnerabilities, delivered with actionable advice for how to protect your organization. For further guidance, contact one of our Kroll experts at one of our 24x7 cyber incident response hotlines or connect with us through our Contact Us page.
The article above was extracted from The Monitor newsletter, a monthly digest of Kroll’s global cyber risk case intake. The Monitor also includes an analysis of the month’s most popular threat types investigated by our cyber experts. Subscription is available below.



