A recent informal survey conducted on our Twitter profile asked security and risk leaders what their biggest concerns were when considering the protection of a predominantly remote workforce due to the COVID-19 pandemic, and 71% of respondents identified personal devices and VPN issues as their biggest concern. This is in part a reflection of the fast transition to work from home operations and the reality that most information security teams had little to no time to adequately prepare. However, the impact can be just as profound for workers who have to adapt to new processes and often, new equipment.
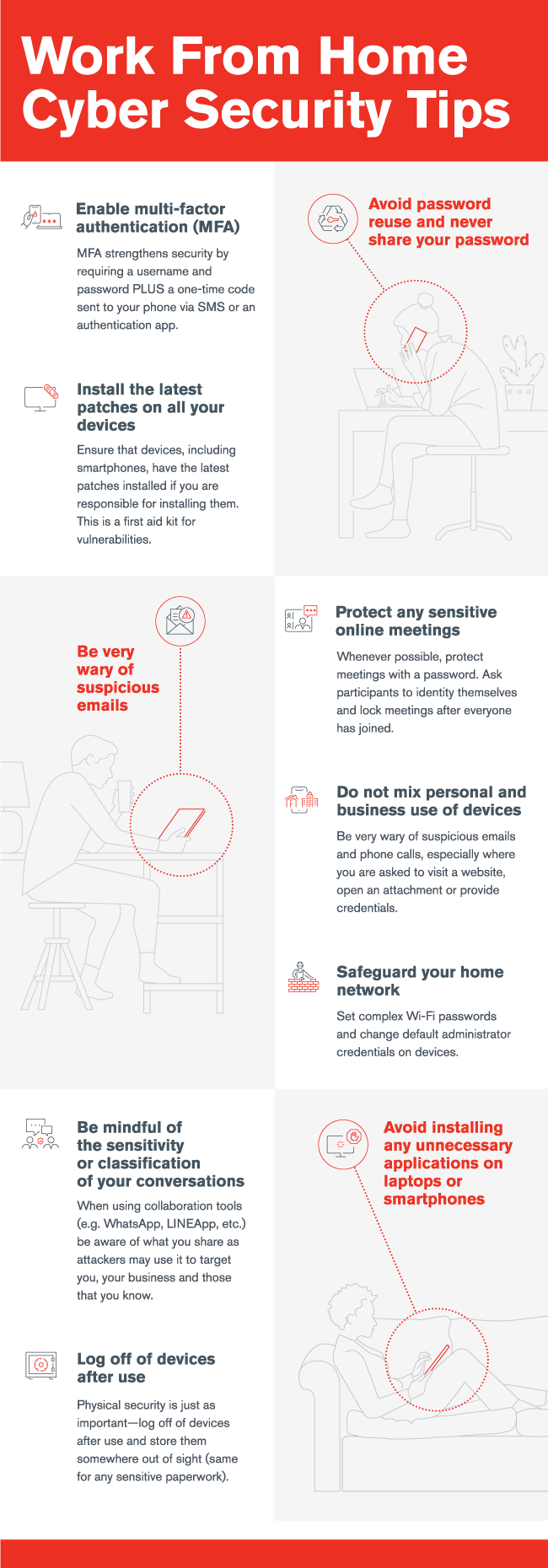
To help information security and risk management teams educate their workers, we compiled a list of 10 fundamental work from home cyber security tips into the infographic below. A high-resolution PDF is also available for download and we encourage its dissemination across your workforce as part of an ongoing effort to build a strong security culture.
Work From Home Cyber Security Tips
As indicated in the infographic, steps to protect remote workers must begin with strengthening their credentials, and multi-factor authentication (MFA) is crucial. Most platforms now offer MFA options, and your company should enforce its use for all sensitive applications.
These efforts are part of a comprehensive security culture program that helps employees internalize a cyber security and data privacy mindset and “own” their role in keeping data safe. Kroll offers Security Culture as a Service, which can be implemented remotely and customized to your specific industry, department or stakeholder roles. Get in touch today.
