
Phishing schemes are always evolving. This past year, email thread hijacking took phishing to new depths of subterfuge as criminals hid in plain sight within existing conversations. But no matter how well cybercriminals have refined their messaging or counterfeited legitimate logos and branding, the one constant has always been their delivery method: email.
Until now. Online chat services have become a new target for cybercriminals to introduce documents loaded with malware into organizations. In Kroll’s investigative experience, the scheme plays out like this:
1. Circumventing Automated Support Systems
Actors know the limitations of online chat services, which commonly draw on a knowledge base of FAQs to answer visitor queries. The actor presents an issue not likely to be covered by the FAQs, and most importantly, one that needs to be resolved by uploading some kind of documentation, e.g., a disputed invoice or photo of damaged merchandise.
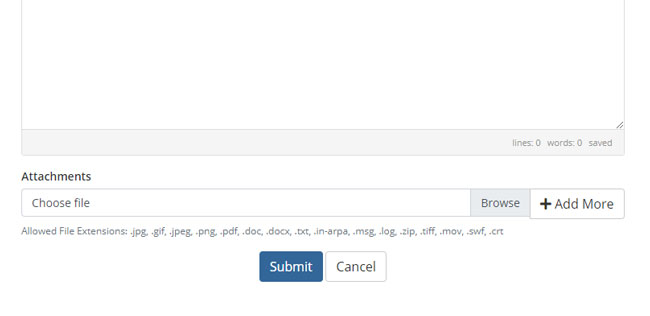
Figure 1 - Example of file upload functionality in support ticket creation
2. Create Ticket with Corrupt File Attachment
A ticket is created in the chat system, complete with a zip file attachment. (Actors usually send zip files because antivirus software does not usually detect the malware contained in compressed files).
3. Support Agent Unsuspectingly Extracts Files
The ticket is routed to an unsuspecting user inside the organization, who opens the attachment and unleashes the malware within. In Kroll’s recent experience with this fact pattern, the malware often provides remote access for actors to ultimately leverage the user’s computer as their beachhead to further their intrusion into the victim network with an eye either on data theft (data exfiltration) or a ransomware attack, sometimes within mere hours.
Cyber Security Essentials for Online Chats
Even before the pandemic, organizations were increasingly using live chat to support employees and customers with a variety of tasks. Whether your organization already uses an online chat service or you are considering adding one, here are a few tips that can help protect your environment from chat-related threats:
- Do Your Diligence
Most online chat services are provided by third parties that customize their software for your organization. Determine what security measures they implement when creating tickets with attachments. Likewise, ask what resources they have to assess the security of those attachments. Require a level of security that aligns with your expectations and review the service provider’s security stance on a regular basis to ensure they are maintaining situational awareness by keeping up with evolving threats. - Open Attachments in a Sandboxed Environment
Before forwarding the inquiry to the relevant customer service rep or another internal resource, direct all tickets with attachments to trained staff to open in a controlled environment and assess the safety of the contents. Consider rejecting all attachments consisting of zip files and require individual files instead. - Protect the Enterprise With Antivirus and/or Endpoint Threat Detection Software
Early detection of malware can help prevent a bad situation from escalating to a crisis. Ensure processes are in place to guarantee timely updating of antivirus software and consider how your organization can collect telemetry from customer support systems. - Consider Using Fill-in Forms
Rather than accepting attachments, consider technology that allows a user to fill in fields and paste in scanned images of documents/photos that might otherwise be sent as an attachment. - If Attachments Are Necessary, Bolster Security Around the Users Receiving the Attachments
This includes their email accounts, their computers and their technical knowledge and training to know what to do with suspicious files and to leverage a dedicated, separate virtualized desktop environment for that activity. - Test Your Online Chat Security
If you currently offer an online chat option, a vulnerability assessment and/or penetration test can offer peace of mind and highlight opportunities to strengthen your security posture.
Delivering superior service to prospective and existing clients, as well as employees, is an important goal for organizations of all kinds. Online live chat has emerged as one strategy for delivering a quick response for the most asked questions while helping staff focus on more complex issues. But as they always do, cybercriminals have discovered the weaknesses that make this channel ripe for phishing. Organizations should be aware of the threat posed by online chat phishing and act now to close that window as soon as possible.
Stay Ahead with Kroll
Cyber and Data Resilience
Kroll merges elite security and data risk expertise with frontline intelligence from thousands of incident responses and regulatory compliance, financial crime and due diligence engagements to make our clients more cyber- resilient.
Data Recovery and Forensic Analysis
Kroll's expertise establishes whether data was compromised and to what extent. We uncover actionable information, leaving you better prepared to manage a future incident.
Malware and Advanced Persistent Threat Detection
Our expertise allows us to identify and analyze the scope and intent of advanced persistent threats to launch a targeted and effective response.
Office 365 Security, Forensics and Incident Response
Digital forensic experts investigate hundreds of Office 365 incidents per year and help strengthen your security.
24x7 Incident Response
Kroll is the largest global IR provider with experienced responders who can handle the entire security incident lifecycle.
Computer Forensics
Kroll's computer forensics experts ensure that no digital evidence is overlooked and assist at any stage of an investigation or litigation, regardless of the number or location of data sources.
