Background of NoSQL database attacks
Beginning in late December 2016, information security researchers began receiving notifications that NoSQL databases, such as MongoDB and Elasticsearch, had been wiped and data replaced with a ransom note. During initial analysis, database administrators were discovering ransom notes demanding payments of up to 1 bitcoin (“BTC”) to recover data. Figure 1 provides a sample of a ransom note found within a compromised MongoDB instance:
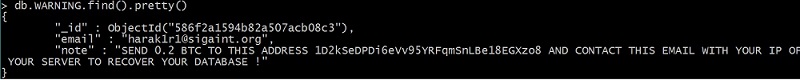
Figure 1: Sample MongoDB ransom note
Unfortunately, the simplicity of this cyber-attack allowed for rapid propagation throughout the internet. Older versions of NoSQL databases provided weak default security settings, oftentimes running unauthenticated with open access to any IP address. Additionally, databases are shipped with web-based APIs that allow for easy data creation, modification, and deletion.
As the attacks spread, organizations that paid ransoms were receiving either partial or no data in return. Additionally, the ease and opportunity of the attack spawned dozens of additional attackers – sometimes overriding already-wiped databases with their own ransom message. To date, over 200TB of data has vanished from MongoDB and Elasticsearch databases.
In early January 2017, attackers also began abusing unauthenticated Hadoop Distributed File System (“HDFS”) control panels. Hadoop clusters are often deployed to house large amounts of data, often in the dozens to hundreds of terabytes. Attackers are not leaving ransom messages in Hadoop clusters; instead they are simply deleting data and creating a directory saying victims should secure their instances.
If you have been compromised
If you find that your NoSQL database has been compromised, please take the following steps:
- Do not perform any further activities on the system, if possible. Depending on the server, there is the potential for data recovery.
- Immediately archive database and firewall logs around the time of the incident.
- Determine if data backups exist that can be restored. Implement security controls prior to data restoration.
- If no backups exist, contact a data recovery specialist to determine what may be recovered.
Additional security recommendations
For future NoSQL database implementations, Kroll recommends the following:
- Upgrade to the latest software version or ensure that any security patches are applied.
- Ensure that databases are not running under the context of privileged accounts, such as root.
- Ensure that two-factor authentication is required for access to data. If possible, also enable role-based access controls.
- If possible, implement firewall rules that restrict access to only known-good IP addresses.
- Perform regular backups of production databases or utilize built-in fault-tolerant mechanisms to prevent total data loss.
- Follow security recommendations of your NoSQL database provider.
NOSQL database security advisories:
Stay Ahead with Kroll
Forensic Investigations and Monitorships
The Kroll Investigations, Diligence and Compliance team consists of experts in forensic investigations and intelligence, delivering actionable data and insights that help clients worldwide make critical decisions and mitigate risk.